Control and help secure email, documents, and sensitive data that you share outside your company walls. From easy classification to embedded labels and permissions, enhance data protection at all times with Azure Information Protection—no matter where it’s stored or who it’s shared with.
See the top 5 tips for information protection
Get an in-depth view of how to protect data in motion
Prepare your organization for a successful adoption strategy
Classify data based on sensitivity and add labels—manually or automatically.

Encrypt your sensitive data and define usage rights when needed.

Apply protection easily without interrupting your employees normal course of work.

See what’s happening with your shared data to gain more control over it.

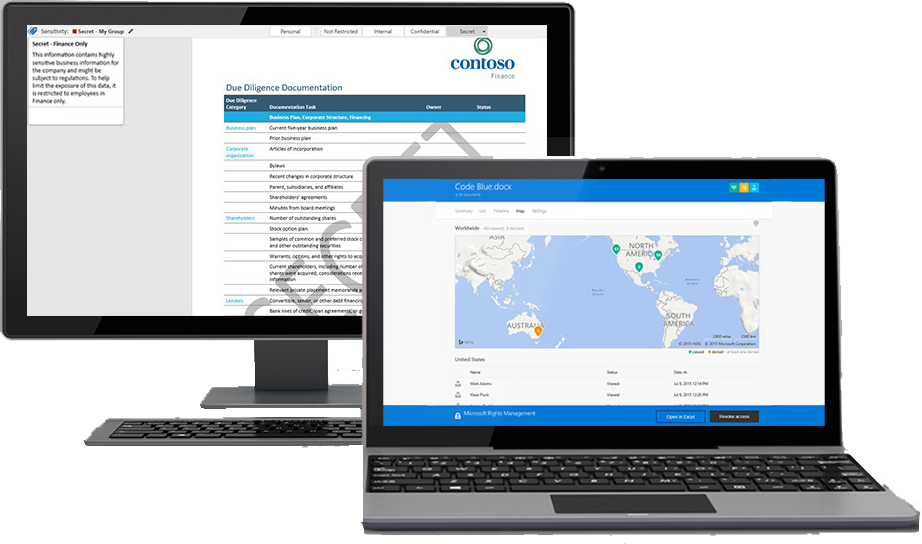
Policies classify and label data at time of creation or modification based on source, context, and content. Classification with Azure Information Protection is fully automatic, driven by users, or based on recommendation.

Embed classification and protection information for persistent protection that follows your data—ensuring it remains protected regardless of where it’s stored or who it’s shared with.
Track activities on shared data and revoke access if necessary. Your IT team can use powerful logging and reporting to monitor, analyze, and reason over data.
Share data safely with coworkers as well as your customers and partners. Define who can access data and what they can do with it—such as allowing to view and edit files but not print or forward.
Data classification and protection controls are integrated into Microsoft Office and common applications to secure the data you’re working on with one click. In-product notifications such as recommended classification help users make right decisions.
Help protect your data whether it’s stored in the cloud or in on-premises infrastructures. You have the flexibility to choose how your encryption keys are managed, including Bring Your Own Key (BYOK) options.